Tromzo Intelligence Graph Delivers a Prioritized Risk View of the Entire Software Supply Chain From Code to Cloud
Intelligence Graph Enables Application Security Teams to Leverage Context From Code to Cloud & Identify Risk Posture of All Software Artifacts
…
MOUNTAIN VIEW, Calif., April 11, 2023 (Newswire.com) - Tromzo, the leader in code-to-cloud risk remediation, today announced Intelligence Graph, as part of the Tromzo Product Security Operating Platform. Building upon the existing automatic asset discovery with ownership, ingestion of vulnerability data, and the ability to prioritize and streamline the remediation of the most significant risks, Intelligence Graph provides a visualization of risk posture for all software artifacts.
Modern development teams deploy code and infrastructure rapidly across a multitude of pipelines, leaving security teams with significant gaps in visibility around who is deploying what artifacts and where. To keep up with this, most security teams have deployed a myriad of security scanning tools that report issues at each layer of the stack. While these security tools generate an overwhelming volume of issues, they also lack context and live in separate data silos making them unactionable. This leads to slower remediation and increased risk.
"With a prioritized risk view of the entire software supply chain with context, organizations can finally understand which few assets are critical to their business, prevent risks from being introduced, and finally automate the remediation lifecycle for the few issues that truly matter," said Harshil Parikh, Chief Executive Officer, Tromzo. "We are excited to bring to market the only unified platform that accurately identifies security and risk posture for all software artifacts from code to cloud."
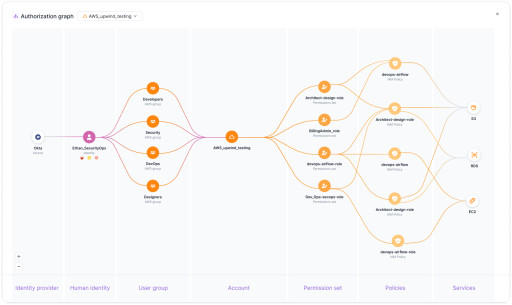
Intelligence Graph visualizes data from development tools such as Code Repositories, CI/CD Platforms, Artifact Registries and Cloud Platforms to accurately identify who is building and deploying what artifacts, and where. This graph-based context along with centralized security vulnerabilities enable application and product security teams to accurately identify security and risk posture for all artifacts from code to cloud.
Intelligence Graph enables Tromzo customers to:
- Prioritize remediation of vulnerable dependencies that have an exploit available, where the dependency has a fix available, is a direct dependency and is in a code repository that is actively deployed to production environments.
- Deduplicate thousands of vulnerabilities in production hosts and containers to automatically identify the root cause fixes in the base images, and automatically assign them to the appropriate team that owns the base images.
- Automatically identify which code repositories are processing PCI/PII/TIN relevant information, and prioritize the vulnerabilities identified on those code repositories from your existing SAST/SCA scanners.
To learn more about Intelligence Graph and how leading with context is necessary, join Ty Sbano, CISO at Vercel, and Harshil Parikh, former CISO and now CEO at Tromzo, on Thursday, May 11, for a LinkedIn Live. Register here: https://www.linkedin.com/events/7051337803648888832/about/.
About Tromzo
Tromzo accelerates remediation of risks from code to cloud. By integrating with existing development and security tools, Tromzo builds a comprehensive software artifact inventory and ownership model with intelligent context from code to cloud — enabling users to automate the complete remediation lifecycle of issues that truly matter. Backed by top investors including Innovation Endeavors, Operator Partners, SVCI and 25+ leading CISOs.
For more information, visit www.tromzo.com and follow us on LinkedIn and Twitter.
Contact Information:Holly H
[email protected]
Original Source: Tromzo Intelligence Graph Delivers a Prioritized Risk View of the Entire Software Supply Chain From Code to Cloud